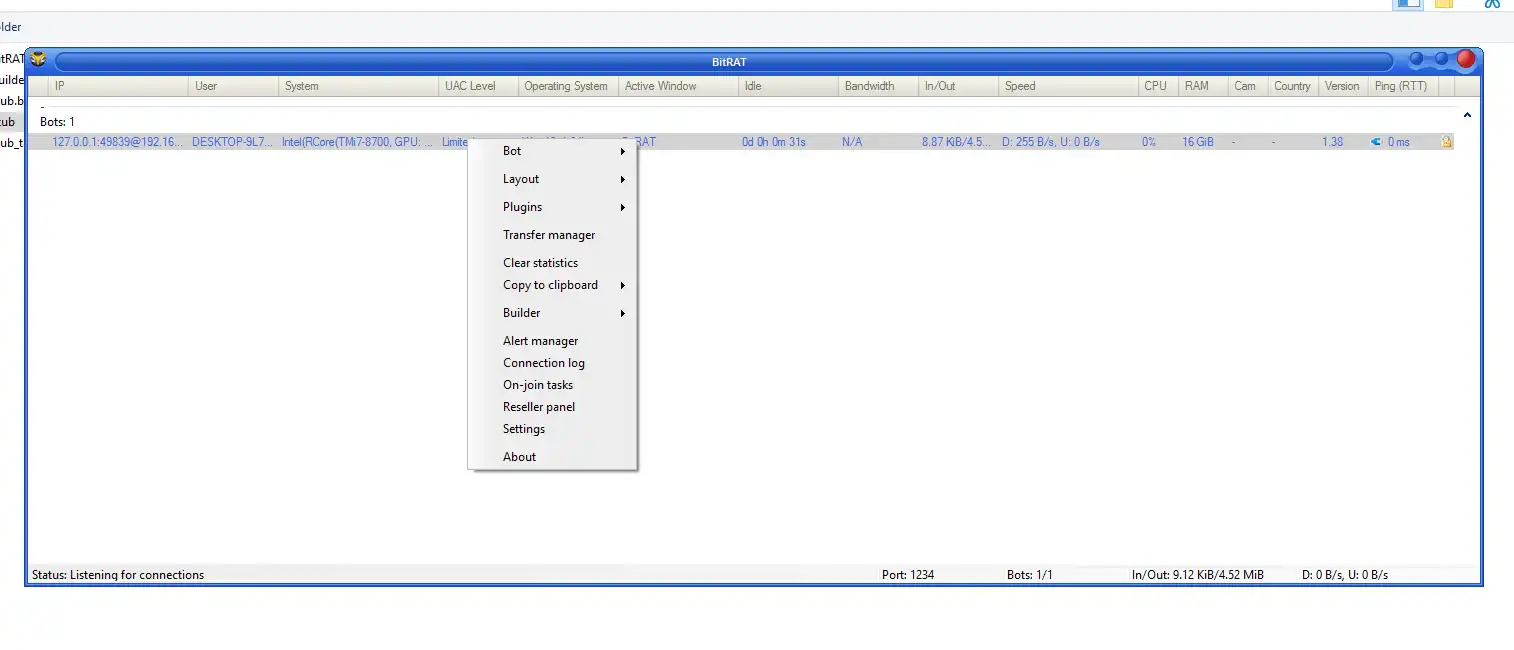
BitRAT 1.39
🖥️ BitRAT 1.39: Advanced Remote Administration Tool – Complete Review BitRAT 1.39 is a feature-rich remote administration tool (RAT) designed to deliver extensive system…
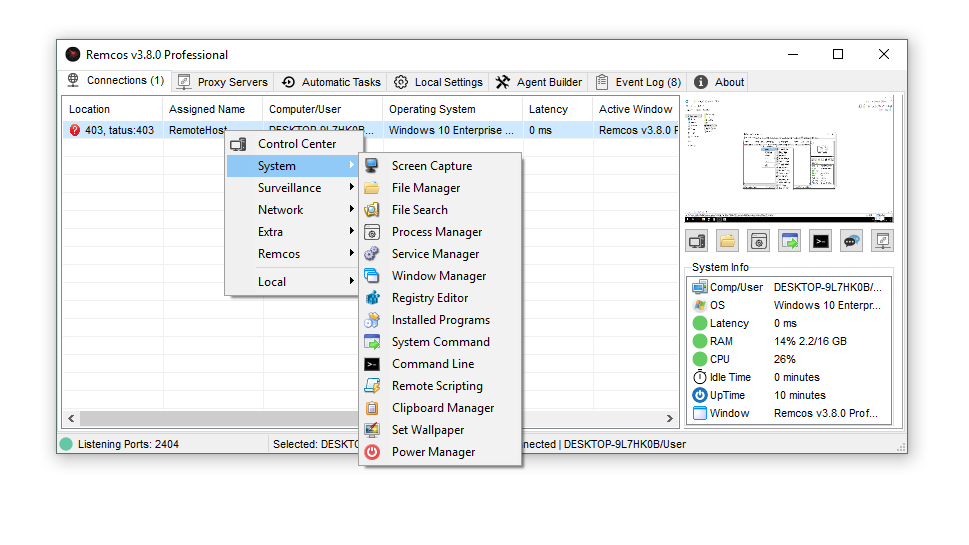
Remcos v3.8.0 Cracked
⚙️ Introduction Remcos v3.8.0 Cracked Remcos v3.8.0 Cracked is an unauthorized version of the legitimate Remote Access Trojan (RAT) software. While the official Remcos…
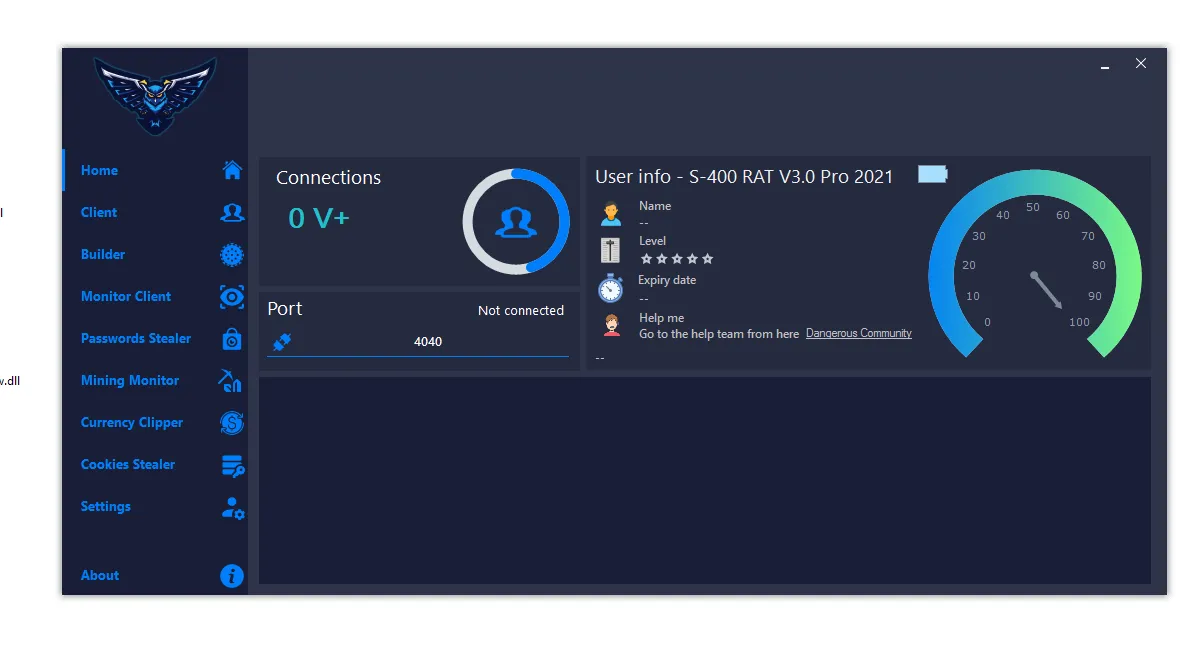
S400 RAT 2026
S400 RAT 2026 (Cracked) – Complete Malware Analysis, Features & Security Risks 🧠 Introduction S400 RAT 2026 S400 RAT 2026 (Cracked) is a highly…
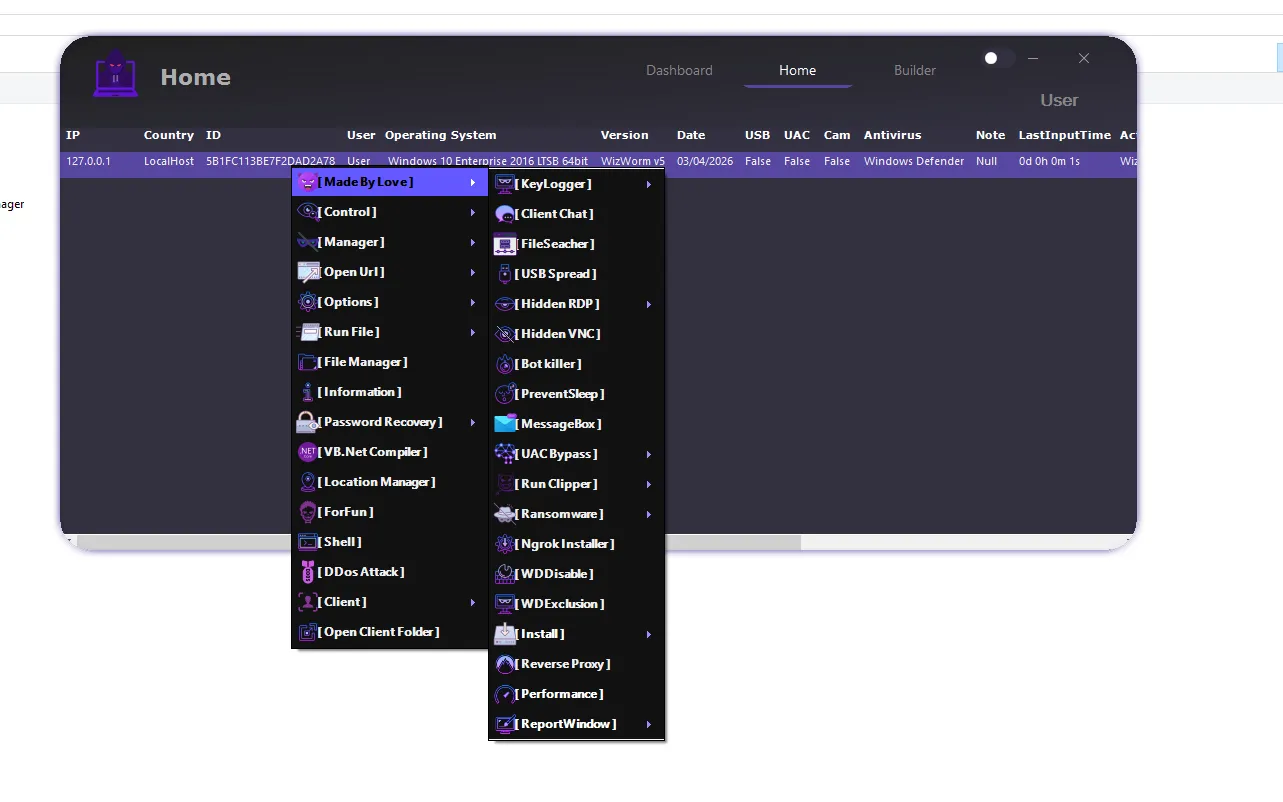
WizWorm V5.0
WizWorm V5.0 Features & Review (2026) – Advanced Remote Administration Tool Guide WizWorm V5.0 is an advanced remote administration and monitoring platform built for…
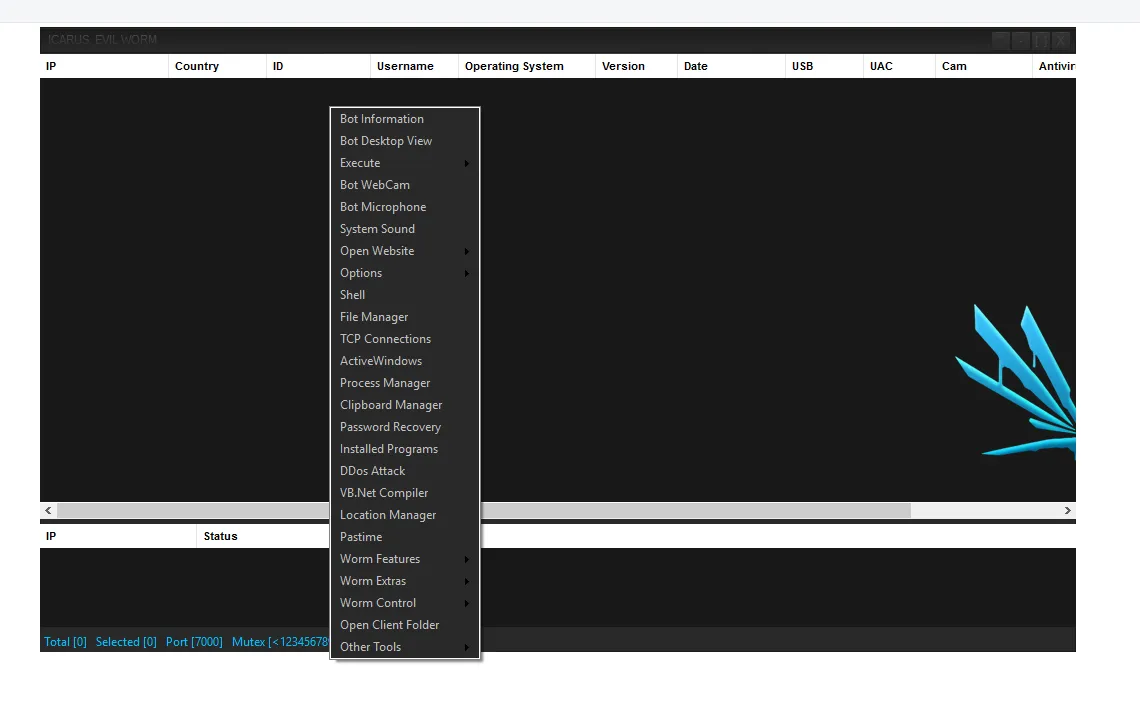
Icarus Evil Worm Cracked 2026
🧠 Introduction The cybersecurity landscape in 2026 has taken a dangerous turn with the rise of Icarus Evil Worm Cracked 2026. Once a premium…
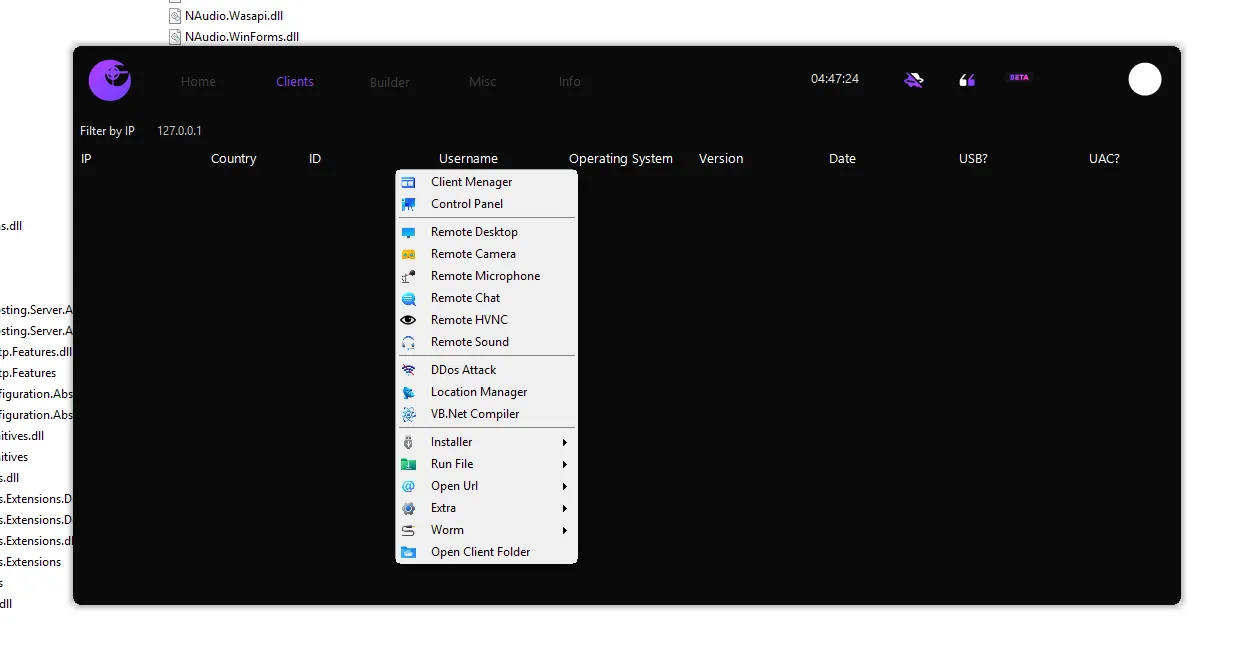
Eclipse RAT 2026 Cracked
🧠 Introduction The rise of Eclipse RAT 2026 Cracked has become a major concern in the cybersecurity world. Originally developed as a premium remote…
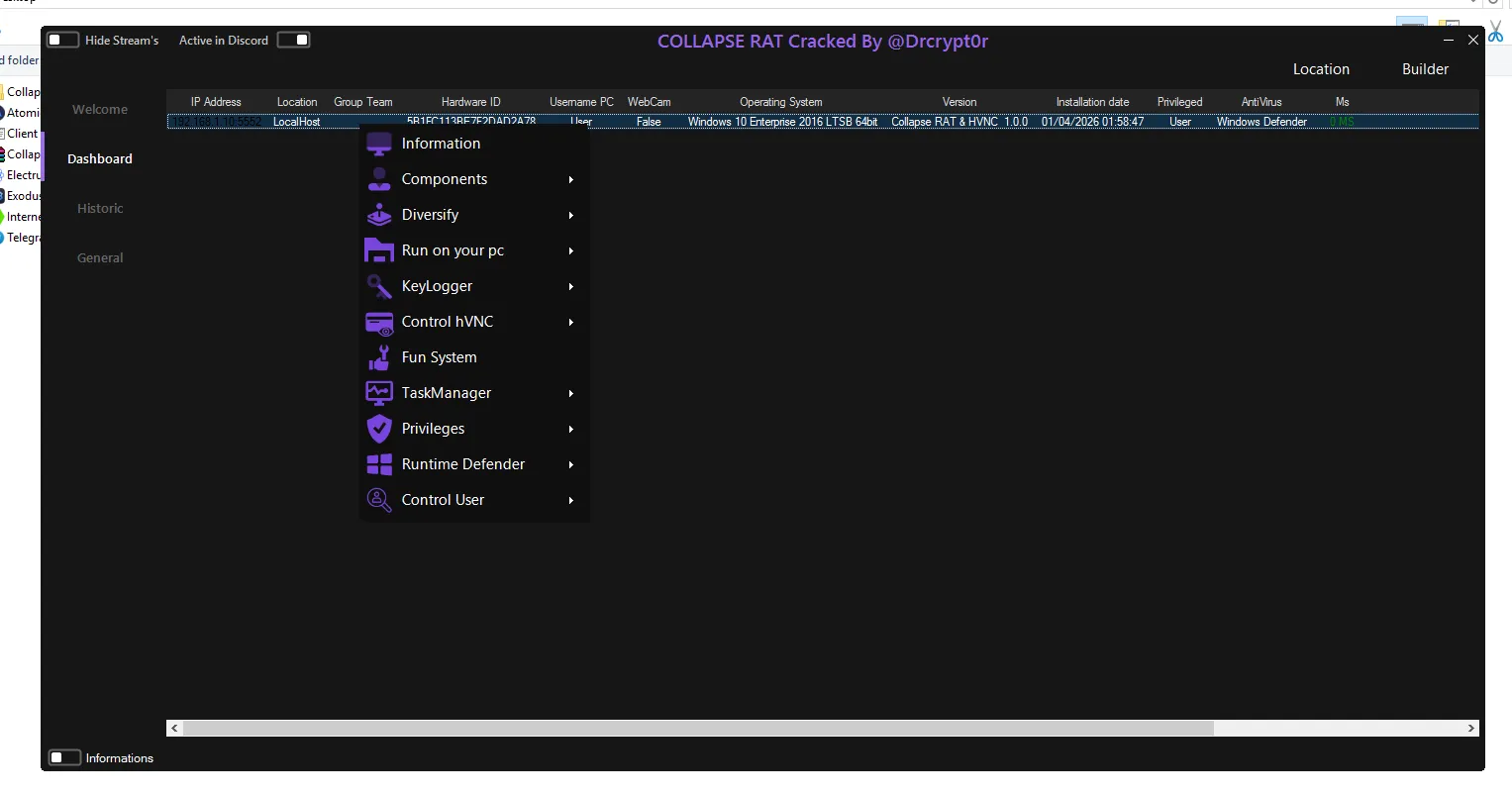
Collapse HVNC RAT 2026
🔍 Introduction In today’s evolving cyber threat landscape, advanced remote access tools are becoming increasingly sophisticated. One such tool gaining attention is Collapse HVNC…
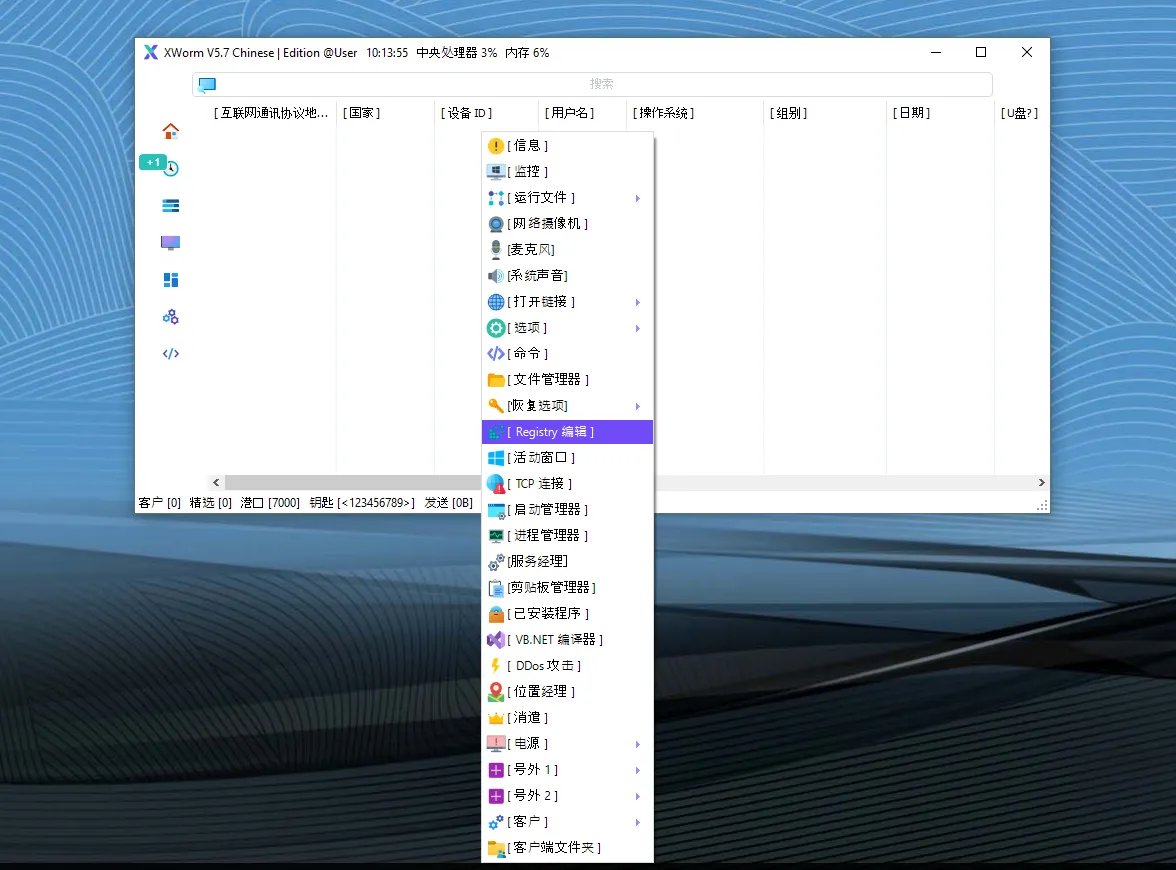
XWorm V5.7 Chinese Edition Cracked
🧲 🔍 Introduction to XWorm V5.7 Chinese Edition Cracked XWorm V5.7 Chinese Edition Cracked is an unofficial, modified, and often illegally distributed version of…
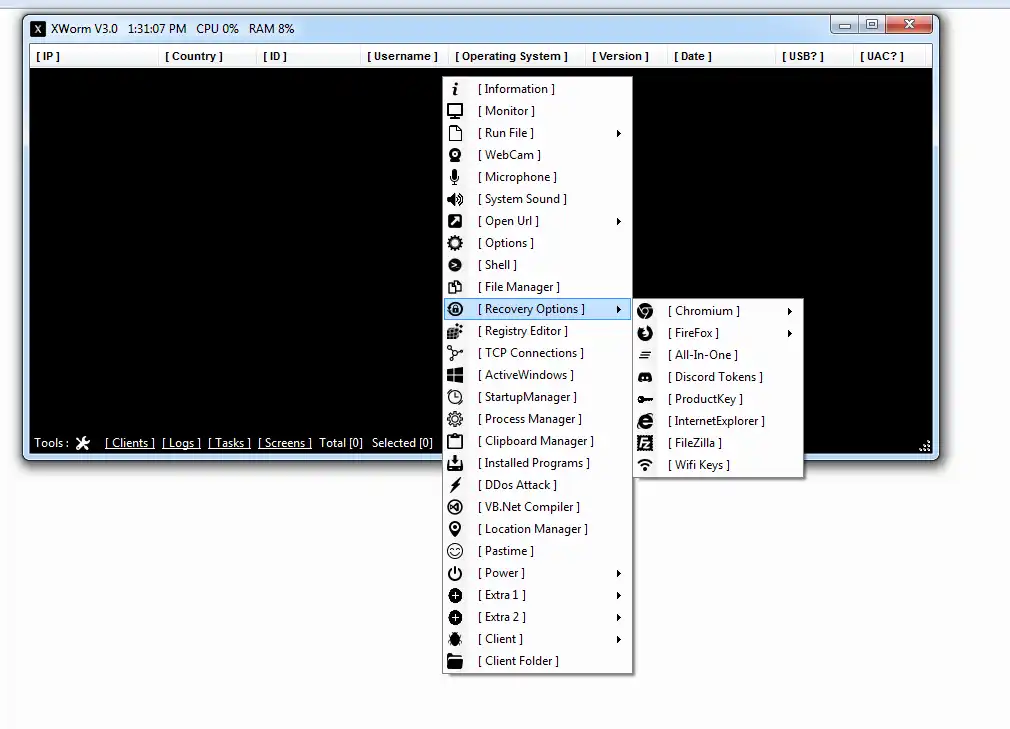
XWORM V 3.0 Cracked
🧠 Introduction to XWORM V 3.0 Cracked XWORM V 3.0 Cracked refers to a modified or illegally distributed version of a Remote Access Trojan…
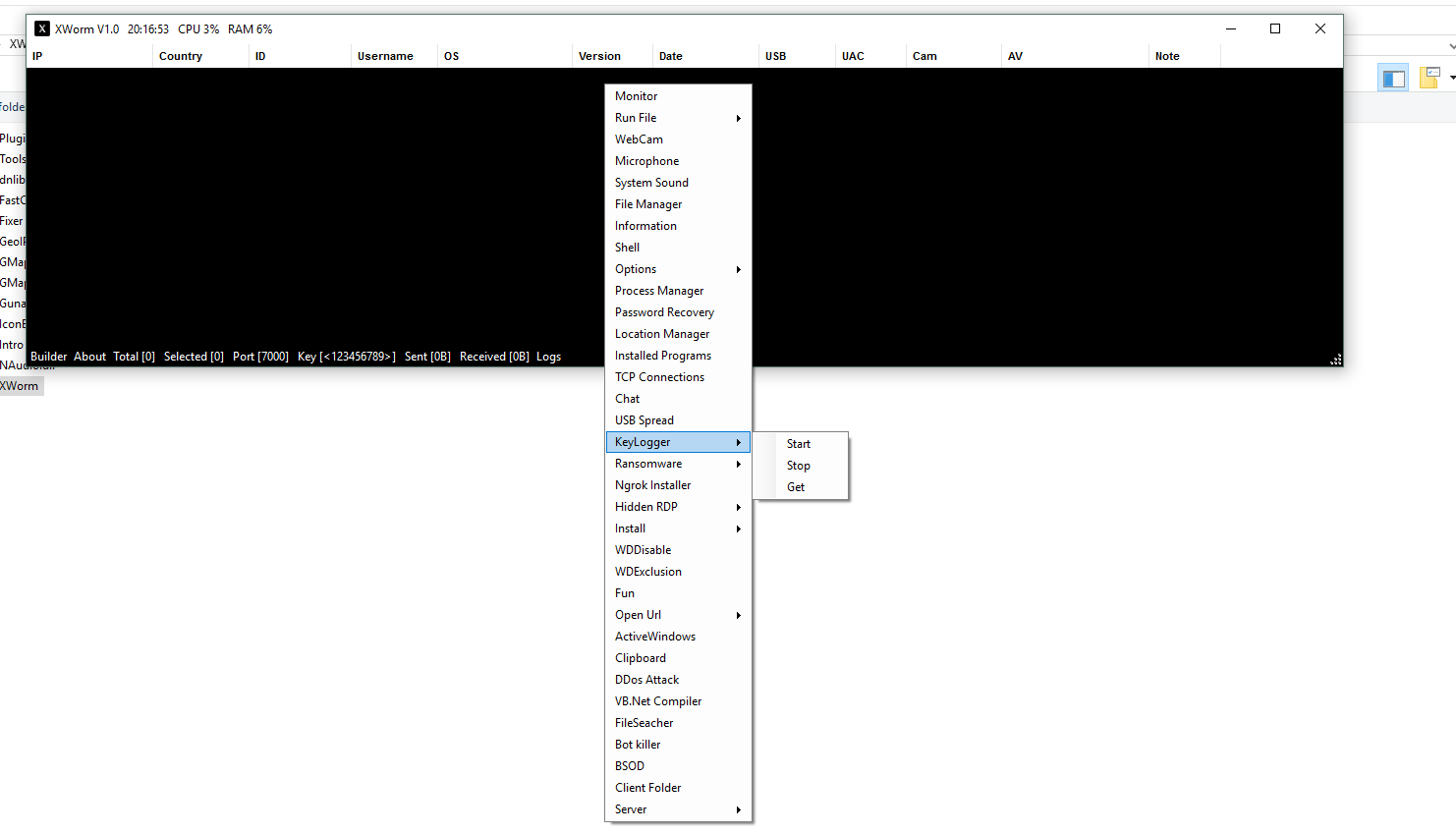
XWorm V 1.0 Cracked
🚨 XWorm V 1.0 Cracked – Complete Guide, Features, Risks & Protection 🧠 Introduction to XWorm V 1.0 Cracked XWorm V 1.0 Cracked refers…