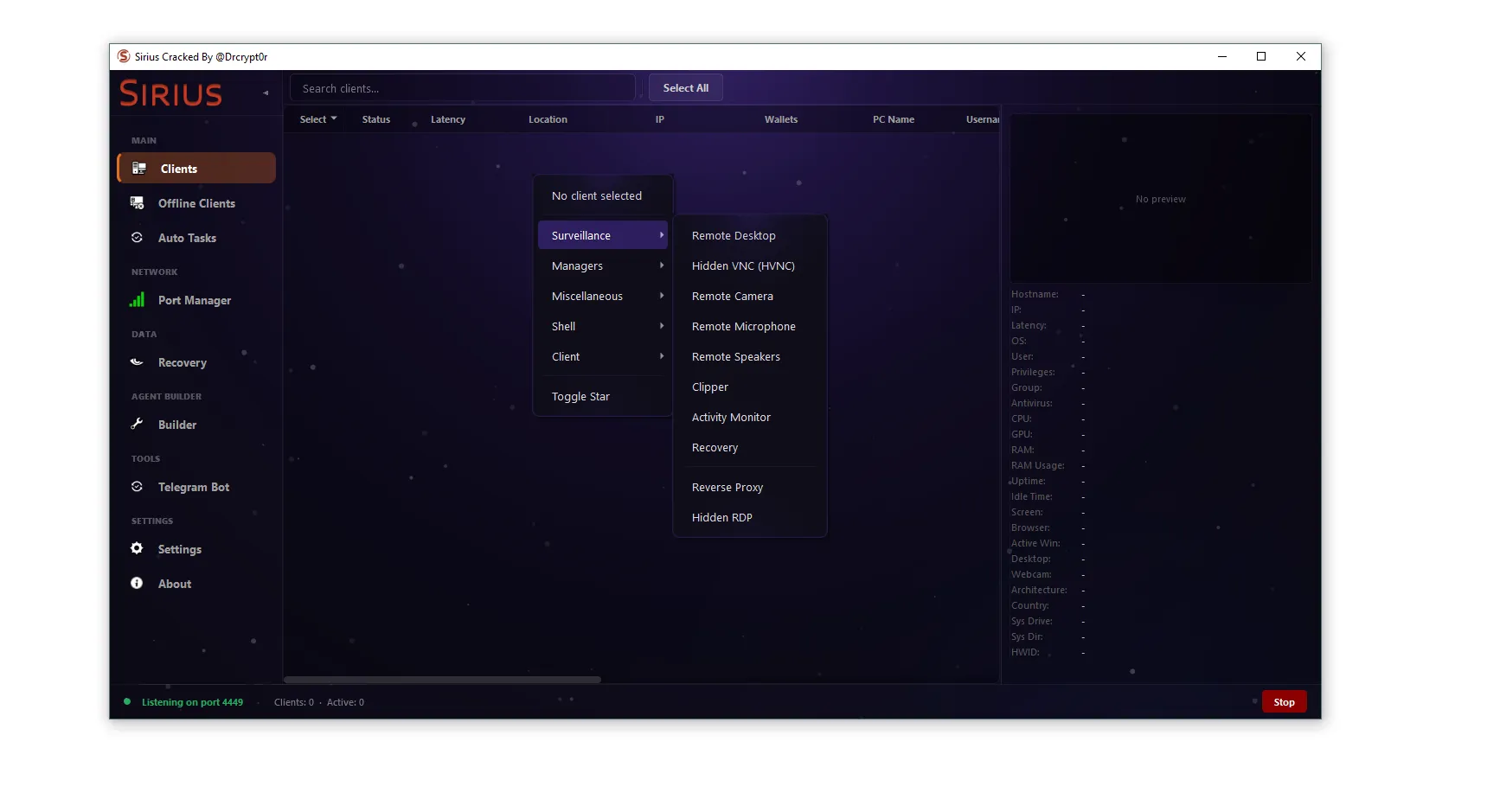
SiriusQT RAT 2026
The rise of advanced cyber threats has made Remote Access Trojans (RATs) one of the most dangerous tools in modern cybercrime. Among them, SiriusQT…
Abko RAT 2026
🛡️ Abko RAT 2026: Complete Cybersecurity Analysis & Defense Guide In today’s rapidly evolving cybersecurity landscape, Remote Access Trojans (RATs) have become one of…
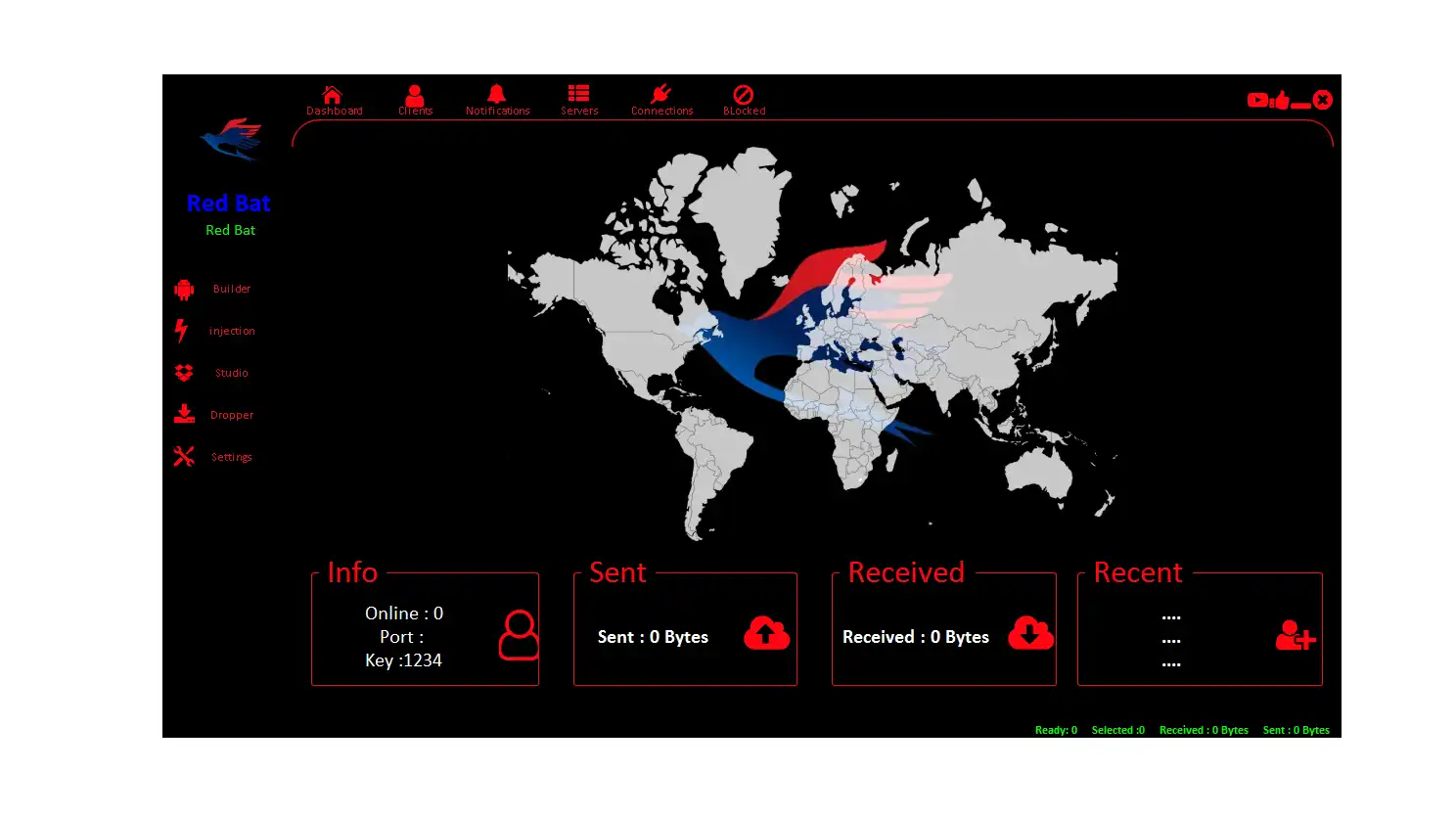
RedBat RAT 2026
📱 Introduction RedBat RAT 2026 The modern mobile ecosystem is facing an unprecedented rise in Android malware, particularly Remote Access Trojans (RATs) like RedBat…
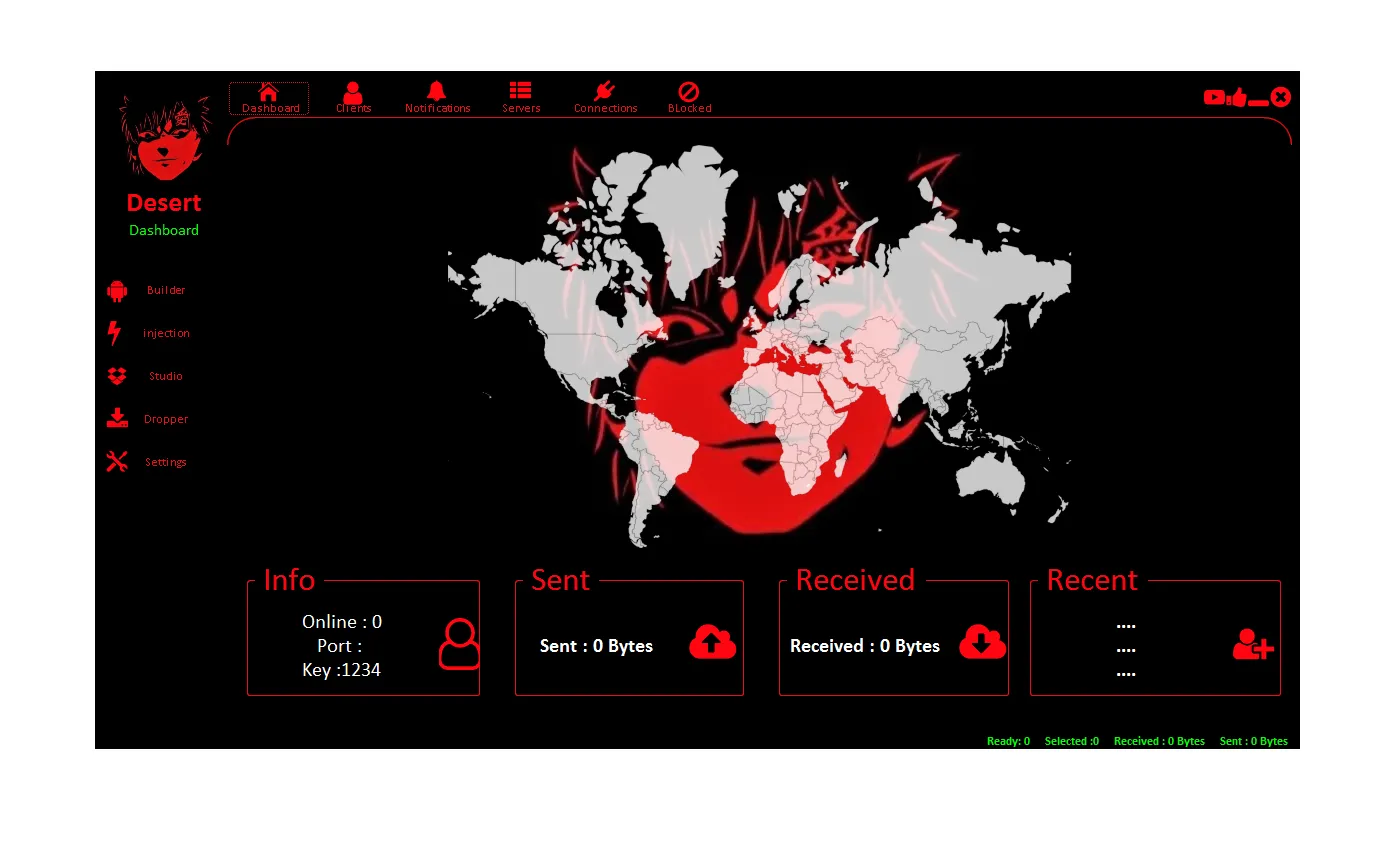
Desert Rat 2026
🐀 Desert Rat 2026: Complete Android Malware Technical & SEO Guide The evolution of mobile cyber threats has accelerated significantly, with Android devices becoming…
Cobra RAT 2026
🐍 Cobra RAT 2026: The Ultimate Guide to Android Malware & Crypto Theft 🔍 🚀 Introduction of Cobra RAT 2026 The mobile cybersecurity landscape…
VIP RAT V 2026
🔥 VIP RAT V 2026 – In-Depth Guide to Android Remote Administration Tools, Risks & Protection As mobile technology continues to evolve, Android devices…
Medusa RAT 2026
🔥 Medusa RAT 2026: Complete Android Malware Analysis, Features, and Security Risks 📱 Introduction: Understanding Medusa RAT 2026 Medusa RAT 2026 is a next-generation…
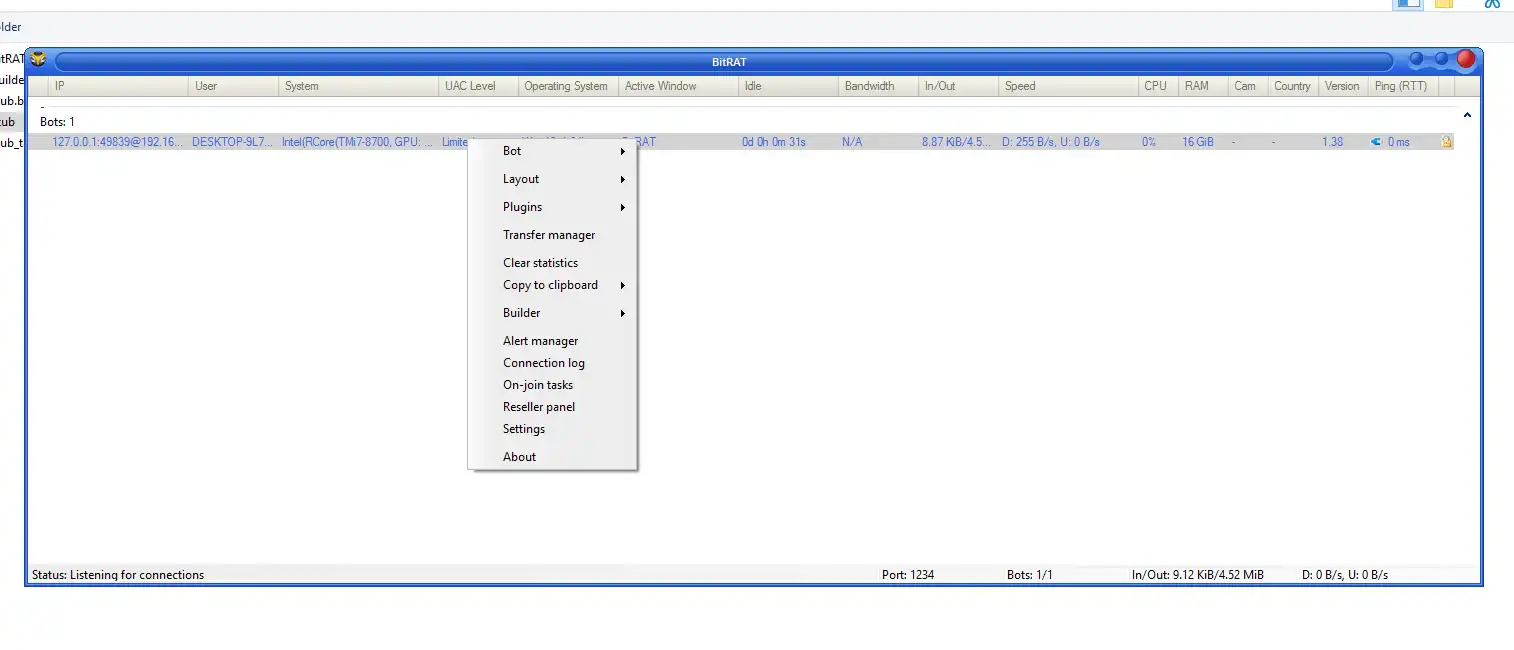
BitRAT 1.39
🖥️ BitRAT 1.39: Advanced Remote Administration Tool – Complete Review BitRAT 1.39 is a feature-rich remote administration tool (RAT) designed to deliver extensive system…
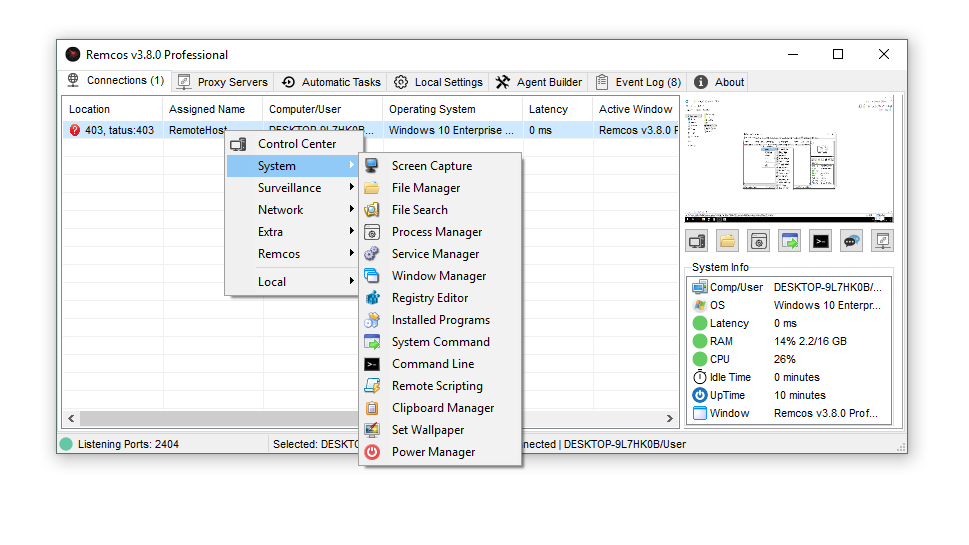
Remcos v3.8.0 Cracked
⚙️ Introduction Remcos v3.8.0 Cracked Remcos v3.8.0 Cracked is an unauthorized version of the legitimate Remote Access Trojan (RAT) software. While the official Remcos…
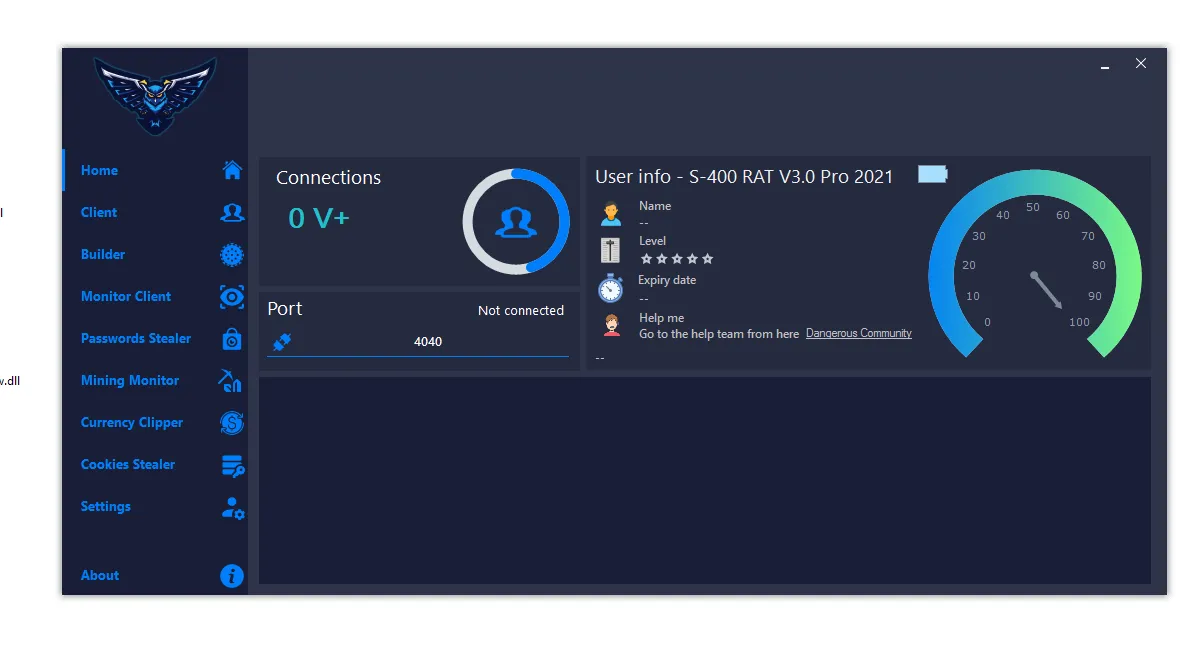
S400 RAT 2026
S400 RAT 2026 (Cracked) – Complete Malware Analysis, Features & Security Risks 🧠 Introduction S400 RAT 2026 S400 RAT 2026 (Cracked) is a highly…